Security Management
The Role of SIEM in Cybersecurity Management
In today’s interconnected world, businesses face a range of risks from various sources like espionage and fraud. To tackle these threats effectively, cybersecurity management implements a variety of strategies. These include creating strong rules, using legal measures, deploying advanced technology defenses, putting procedural safeguards in place, and educating employees through comprehensive cybersecurity training programs. Among these defenses, Security Information and Event Management (SIEM) plays a crucial role in enhancing the efficiency and productivity of Cyber Security Management. By centralizing data security and identity access management solutions, SIEM simplifies threat detection, response, and compliance, ensuring a strong defense against digital risks.
Why SIEM?
SIEM stands as an indispensable pillar in cybersecurity management for its prowess in threat detection and response, centralized monitoring capabilities across diverse systems, aiding compliance adherence, facilitating incident investigation and forensics, integrating threat intelligence feeds for proactive defense, and streamlining operational efficiency through automation. SIEM’s ability to aggregate, correlate, and analyze security events in real-time provides organizations with the critical visibility needed to identify anomalies, respond swiftly to security incidents, meet regulatory requirements, conduct thorough forensic analysis, and stay ahead of emerging threats, ultimately fortifying their defenses and safeguarding valuable assets against evolving cyber risks.
How does SIEM work?
In simple terms, Security Information and Event Management (SIEM) tools gather, organize, and sort data to spot threats and meet data regulations. Although these tools may differ in features, they generally share common functions: collecting and organizing data to detect risks and ensure compliance with data rules.
Log management
Log management in Security Information and Event Management (SIEM) involves the comprehensive process of collecting, storing, and analyzing logs from various security devices within a network. These logs serve as digital footprints, documenting system activities, potential security breaches, and user interactions. By centralizing this data, SIEM log management enables real-time monitoring, threat detection, compliance auditing, and investigative analysis. Through the aggregation of logs from devices like firewalls and intrusion detection systems, SIEM creates a centralized repository where data is indexed for easy retrieval and analysis. This process empowers administrators to swiftly identify anomalies, investigate suspicious behavior, and enhance overall security strategies based on historical log data. SIEM log management is instrumental in fortifying cybersecurity defenses, enabling organizations to proactively detect malicious activities, mitigate security vulnerabilities, ensure regulatory compliance, and respond effectively to cyber threats. Ultimately, an effective log management system within a SIEM framework is essential for maintaining a robust security posture in today’s digital landscape.
Event correlation and analytics
Event correlation and analytics in the realm of IT involve the meticulous examination of events within an IT infrastructure to unveil connections between them, pinpoint issues, and determine their underlying causes. This process is pivotal for detecting problems efficiently and effectively. By leveraging event correlation tools, organizations can enhance their systems’ and applications’ monitoring capabilities, leading to better uptime and performance. In the context of a Security Information and Event Management (SIEM) solution, event correlation plays a critical role. Through the application of sophisticated analytics that can recognize complex data patterns, event correlation offers valuable insights that aid in swiftly identifying and mitigating potential security threats to the organization. SIEM solutions play a crucial role in bolstering IT security teams’ mean time to detect (MTTD) and mean time to respond (MTTR) metrics by streamlining the analysis of security events and reducing manual workflows, ultimately enhancing the overall security posture of the organization.
Incident monitoring and security alerts
Incident monitoring and security alerts are crucial aspects of a Security Information and Event Management (SIEM) system. SIEM streamlines its analysis by compiling all the information into a single centralized dashboard. This dashboard serves as a command center for security teams to keep a close eye on system activity, assess alerts, pinpoint potential threats, and kickstart responses or fixes.
Within these dashboards, real-time data visualizations are often incorporated to help security analysts detect sudden spikes or patterns in suspicious behavior. By using preset correlation rules that can be customized, administrators receive instant alerts when concerning activities are detected. This immediate notification enables them to take prompt actions to address and neutralize threats before they escalate into more serious security breaches. In essence, SIEM not only provides a comprehensive view of the security landscape but also equips organizations with the tools to proactively respond to emerging threats, thereby bolstering their overall cybersecurity defenses.
Compliance Management and Reporting
With Security Information and Event Management (SIEM) systems are essential for organizations adhering to various regulatory standards. SIEM tools are favored for their automated data collection and analysis capabilities, making them invaluable for ensuring compliance across the entire business infrastructure.
One key strength of SIEM solutions is their ability to generate real-time compliance reports tailored to standards like PCI-DSS, GDPR, HIPAA, and SOX. By automating the process of collecting and analyzing data, SIEM lightens the load of security management and aids in the early detection of potential violations. This proactive approach allows organizations to address compliance issues promptly.
Moreover, many SIEM platforms come equipped with pre-configured add-ons that can produce automated reports aligned with specific compliance requirements. These out-of-the-box features streamline the reporting process, saving time and effort for security teams while ensuring that organizations meet the necessary standards to operate securely and legally.
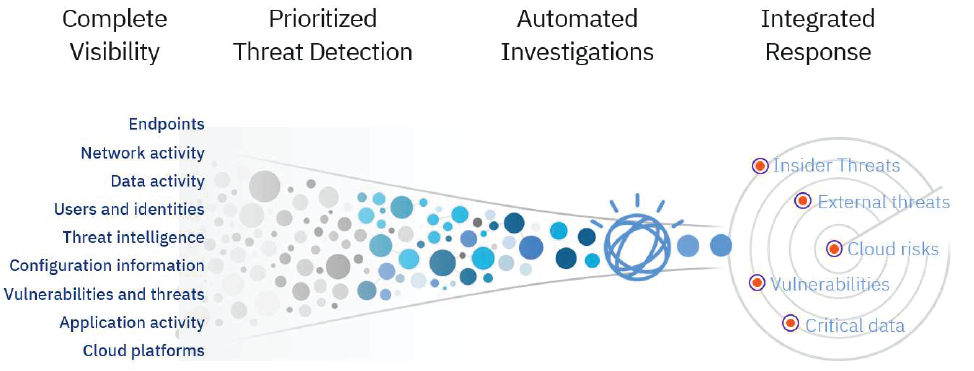
Automate security intelligence to rapidly detect threats
QRadar automatically analyzes and correlates activities from various data sources, such as logs, events, network flows, user actions, vulnerability data, and threat intelligence, to detect both known and unknown threats. (Source: IBM Security QRadar ). Read more in IBM Security QRadar Visibility, detection, investigation, and response.